
Kayo Magalhães / Câmara dos deputados Professor Alcides é o relator da proposta A Comissão

Kayo Magalhães / Câmara dos Deputados O deputado Gabriel Nunes vai presidir o colegiado Foi

Kayo Magalhães / Câmara dos Deputados Delegado Paulo Bilynskyj é o relator da proposta A

Vinicius Loures/Câmara dos Deputados Ana Paula: atuação feminina cresce a cada ano, inclusive na gestão
Mas conhecer as ferramentas não significa usá-las de fato no cotidiano: apenas 46% das micro e

O levantamento revela, ainda, que os consumidores que pretendem comprar presentes em pequenos negócios planejam

O novo Siri AI da Apple, revelado ontem na Worldwide Developers Conference anual da Apple (WWDC 2026), pode parecer uma história de produto de consumo superficialmente. Mas para desenvolvedores corporativos e líderes de TI, a maior novidade da WWDC26 é que a Apple está transformando a Siri em uma interface de IA de todo o sistema para aplicativos, dados e ações no local de trabalho no iPhone, iPad, Mac, Apple Watch e Vision Pro, conforme revelado no guia do desenvolvedor WWDC26 Apple Intelligence. Em outras palavras, se sua empresa oferece um aplicativo em dispositivos Apple, seja ele servido em dispositivos móveis iOS ou Mac, a nova Siri AI pode forçá-lo a mudar a forma como esse aplicativo é descoberto, servido e seus conteúdos e fluxos de trabalho disponibilizados aos usuários finais. Os desenvolvedores corporativos podem expor o conteúdo do aplicativo por meio de App Entities, disponibilizá-lo para o índice semântico Spotlight da Apple, definir ações por meio de App Intents e App Schemas e mapear elementos da interface do usuário na tela para objetos de aplicativo por meio de View Annotations. Isso torna o Siri AI muito mais do que um assistente de voz. A Apple está posicionando-o como uma ação de aplicativo alimentada por IA e uma camada de descoberta de conteúdo integrada em seus sistemas operacionais. Siri se torna uma camada de ação do aplicativo Para os desenvolvedores empresariais, a mudança pode ser significativa. Um aplicativo de negócios que adote adequadamente as novas estruturas da Apple poderia permitir que os usuários pedissem à Siri para encontrar, resumir, atualizar ou agir de acordo com o conteúdo do aplicativo sem que o desenvolvedor tivesse que construir uma interface de chatbot separada. A Apple diz que App Intents, sua estrutura existente para expor ações de aplicativos a recursos do sistema como Siri e Atalhos, é o caminho para conectar aplicativos ao Apple Intelligence e Siri AI, enquanto os esquemas tornam o conteúdo e as ações do aplicativo utilizáveis por meio de linguagem natural. Em termos práticos, isso poderia se aplicar a registros de clientes em um CRM, tickets abertos em uma central de serviços de TI, tarefas de projetos, faturas, eventos de calendário, documentos, despesas, notas, mensagens ou registros de serviço de campo. Em vez de abrir um aplicativo, pesquisar manualmente e clicar nos menus, um funcionário pode pedir à Siri para agir no objeto específico que está visualizando ou recuperar um item relacionado de outro aplicativo. Spotlight se torna o gancho de pesquisa empresarial A Apple diz em seu guia Apple Intelligence WWDC26 que os esquemas de entidade contribuem com o conteúdo do aplicativo para o índice semântico do Spotlight, enquanto os esquemas de intenção permitem que os usuários tomem medidas sobre esse conteúdo indexado sem que os desenvolvedores definam uma lista rígida de frases de comando. A Apple também afirma que a nova API View Annotations permite que os desenvolvedores mapeiem visualizações para entidades para que os usuários possam consultar o que está na tela de forma conversacional – por exemplo, “resumir este tópico do cliente”, “adicionar esta fatura às minhas despesas” ou “acompanhar esta tarefa amanhã”. Essa é uma distinção importante das integrações anteriores de assistentes de voz, que muitas vezes exigiam estruturas de comando estreitas e frases de invocação explícitas. Em vez disso, a Apple está oferecendo aos desenvolvedores uma maneira de descrever os dados e recursos de um aplicativo para que Siri, Spotlight e Shortcuts possam usá-los por meio do sistema. Os desenvolvedores obtêm ferramentas de teste para Siri e ações de aplicativos A Apple também está adicionando AppIntentsTesting, uma estrutura que valida App Intents por meio da mesma infraestrutura usada por Siri, Shortcuts e Spotlight sem exigir automação de UI. Isso é importante para as equipes de software empresarial porque as ações de aplicativos em linguagem natural precisam ser testáveis, repetíveis e confiáveis antes de serem confiáveis nos fluxos de trabalho de produção. Ele também oferece aos desenvolvedores um caminho para incluir o comportamento do Siri e do Spotlight em pipelines de teste comuns, em vez de tratar a integração do assistente como um recurso de demonstração manual. O resultado é um mandato mais claro para o desenvolvedor: se um aplicativo quiser aparecer bem dentro da Siri AI, provavelmente precisará expor seus dados, ações e contexto na tela por meio das estruturas de sistema da Apple. Para os fornecedores empresariais de SaaS, isso poderá tornar-se uma parte importante da competitividade da plataforma Apple, especialmente em categorias como produtividade, colaboração, CRM, gestão de projetos, finanças, design, gestão de conhecimento, saúde, logística e operações de campo. Apple expande sua pilha de modelos para desenvolvedores A Apple também está usando o WWDC26 para expandir sua pilha de desenvolvedores de IA além do Siri. A estrutura Foundation Models atualizada dá aos desenvolvedores Swift acesso aos modelos no dispositivo da Apple, modelos da Apple executados por meio de computação em nuvem privada e provedores de modelos terceirizados que estão em conformidade com o protocolo Language Model da Apple. Isso dá aos desenvolvedores mais flexibilidade do que um único caminho de modelo exclusivo da Apple. A Apple afirma em seu guia do desenvolvedor Apple Intelligence que a estrutura agora oferece suporte a prompts multimodais, ferramentas de visão, perfis de modelos dinâmicos e avaliações. Em teoria, um aplicativo corporativo poderia usar um modelo no dispositivo da Apple para tarefas privadas ou leves, chamar o Private Cloud Compute da Apple para um raciocínio mais pesado ou conectar um provedor externo como Claude, Gemini, um modelo de código aberto ou um modelo controlado pela empresa através da interface modelo-provedor da Apple. Core AI traz modelos personalizados para o silício da Apple A Apple também está introduzindo o Core AI, uma estrutura em nível de sistema operacional para executar modelos dos próprios desenvolvedores no silício da Apple. Para empresas que não desejam que dados confidenciais sejam enviados para um modelo de nuvem, a inferência local continua sendo uma das vantagens mais importantes da Apple. Core AI oferece aos desenvolvedores uma maneira original de implantar

Fundada pela cientista da computação Mariana Soares, a Auter Airports surge para integrar operações, reduzir a fragmentação dos aeroportos regionais e apoiar uma

Apresentado por Norton Durante 39 dias neste verão, o planeta fará aproximadamente a mesma coisa ao mesmo tempo. A Copa do Mundo de

Atuação de Júlia Silva em iniciativas ligadas à transformação digital, engenharia e inclusão em STEM chama atenção em universidades e empresas americanas A

Nosso sistema fez uma coisa, e funcionou bem: transformou perguntas de linguagem natural em chamadas de API. Os usuários eram analistas, gerentes de

A Agentic AI é agora uma parte essencial do processo de engenharia, impulsionando uma enorme alavancagem de execução e nos ajudando a gerar
For three years, Microsoft's artificial intelligence story has been inseparable from OpenAI. The partnership — cemented by a cumulative investment exceeding $13 billion

O cofundador e CEO da Anthropic, Dario Amodei, disse que isso estava chegando, mas ainda parece um marco: mais de 80% do código

Embora muitos fornecedores de modelos de código aberto de IA busquem modelos maiores e mais poderosos, o Google ainda está prestando atenção ao

O árbitro somali Omar Artan, a quem foi negada a entrada nos Estados Unidos para apitar a Copa do Mundo, foi nomeado para

Bandeirinhas coloridas, comidas típicas, música ao vivo, clima de quermesse e uma programação pensada para todas as idades. Em junho, o Malai Manso

Por que profissionais brilhantes passam meses sem recolocação e o que uma entrevista realmente avalia Por Fábio Salomon Em quase vinte anos recrutando

Levantar rápido da cama ou da cadeira e sentir a cabeça girar é uma situação bastante comum. Mas por que isso acontece? Segundo
A internet via satélite surgiu como uma alternativa para levar conectividade a regiões onde a fibra óptica e as redes móveis não têm

Artan, eleito o árbitro masculino do ano da Confederação Africana de Futebol (Caf) em 2025, foi um dos 52 árbitros selecionados para a

Kayo Magalhães / Câmara dos Deputados O deputado Gabriel Nunes vai presidir o colegiado Foi instalada na terça-feira (9) a comissão mista que
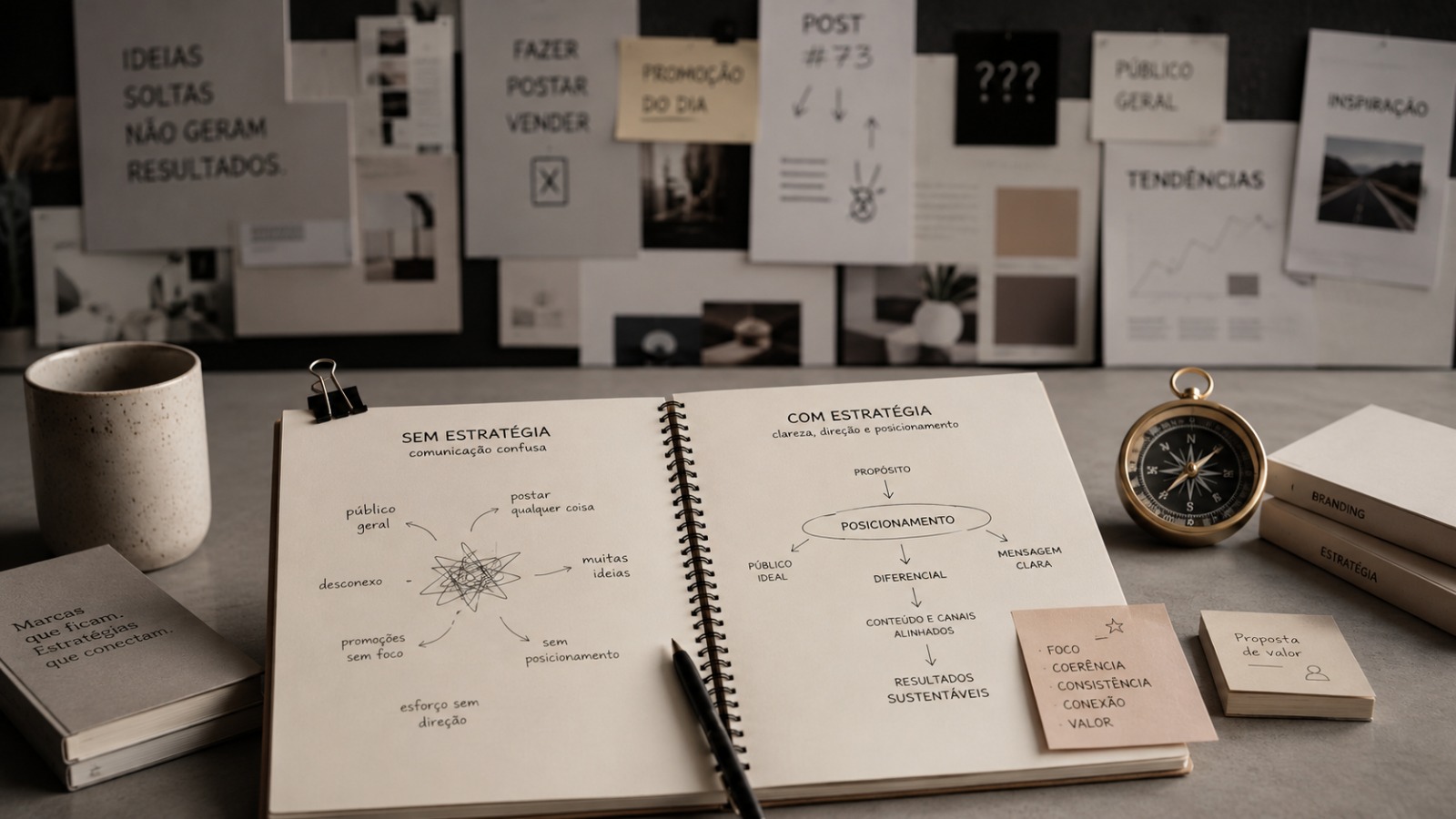
A ausência de planejamento estratégico é apontada como o principal motivo pelo qual pequenas empresas perdem visibilidade e clientes — mesmo tendo bons

A articulista Myrinha Vasconcellos analisa os impactos emocionais invisíveis do WOLLYING e o custo humano da violência psicológica entre mulheres.

Fundador da LV Garage e da Qualytech Blindagens, Vitor construiu uma operação que hoje atende veículos premium, seguradoras e concessionárias após começar lavando

A riqueza de uma nação já não se mede apenas por aquilo que ela produz, mas pela capacidade de produzir conhecimento. Durante muito

Especialista defende que clínicas terapêuticas precisam deixar de atuar apenas como centros de atendimento para se tornarem empresas estruturadas e sustentáveis Durante muitos
© 2025 Todos os direitos reservados a Handelsblatt